You likely have employees who work outside the office at least some of the time, if not working remotely all the time. Therefore, you owe it to yourself and your business to equip your team with the tools and resources they need to be successful. We recommend that you carefully consider the technology you provide for your employees, especially when they work out of the office part of the time, as well as how your team will access these tools and resources.
BNMC Blog
Today, technology stands out for its remarkable pace of growth and continuous innovation. I really mean continuous. Nearly everything that has been developed is eventually improved upon, until something new comes along and replaces it. If an improvement is good enough, especially if it is seen as indispensable, it will often transcend the initial invention. This has happened many times over the years.
Windows has a lot of neat hidden features in its settings, one of which is called Storage Sense. Storage Sense can help you manage some of the more inconspicuous file storage issues you might encounter during your time at the office or on your personal device. Let’s go over what Storage Sense can do and why it’s helpful to keep in mind.
Just like any other piece of machinery or appliance in your household or office, your computer will need regular cleaning to keep it in proper working order. To help you do this, we’ve put together three helpful tips you can use while you’re cleaning your devices. And, of course, if you’re ever uncomfortable doing any of these, we always recommend leaving the work to the professionals, too.
You sometimes see in movies or television shows situations where someone wants to erase the contents of a computing device through the use of magnets, but how much truth is there really to this kind of thing? Today, we dive into just how much a magnet can damage a device and whether or not you need to worry about them.
The average business has countless endpoints accessing their infrastructure’s data at any given point throughout the workday. Think about it; just how many devices have access to your business’ data infrastructure? Do you know the answer? If not, then perhaps you could be doing more to secure these endpoints, as any endpoint that is not adequately secured could be a gateway into your network for a cybercriminal.
Let’s say you are going about your workday when your computer suddenly crashes. Your first reaction might be to reach out for support, and if so, then you are correct; we can’t let you suffer from downtime for too long! Let’s go over what the acquisition of support might entail, even if the problem you are experiencing cannot be solved through a remote support option.
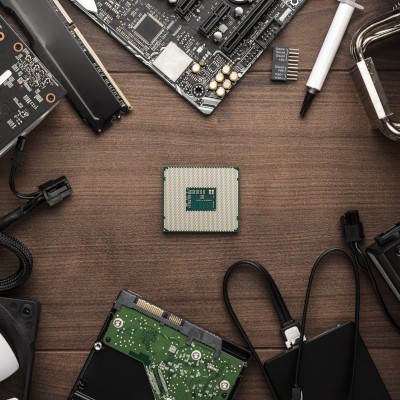
For companies that depend on their computing, the workstation plays an important role. The problem with them is that spending big money on computers that are used for general productivity is not cost effective, but if they don’t have the computing power needed to successfully run the software that your company uses, they won’t do you any good. Today, we will talk a bit about hardware considerations you will need to make when choosing workstation hardware, and the cloud-hosted options that may be a good option for your business.
Workplace stress has become a key issue in today’s business environment, and many studies have been performed to demonstrate why there has been such an increase, as well as what can be done to stymie its impact. Microsoft has recently filed a patent to show how seriously this issue must be taken. While it’s good to see the tech company invested in resolving this issue, one has to wonder whether the help of a new technology solution is necessary in identifying stressors in their workplace environment.
No matter how new a device is, the unfortunate truth is that it will not last forever. Eventually, you will need to replace your device; the question then becomes what you do with your old technology. While you could just throw it in the trash, this is not only wasteful but also a security risk. In order to protect both your personal data and the environment, you must go through the proper channels to make sure that e-waste gets properly disposed of.
With computers being so integral to modern life, it can be too easy to hear about certain drawbacks—like the purported impacts of blue light—and discount them as little more than a way for companies to sell things that nobody really needs. While we aren’t going to speak to all these presumed drawbacks, we did want to spend some time discussing blue light and how it could impact your health (and how to help keep it from doing so).
Notifications are almost ubiquitous in computing nowadays, which is what makes it so surprising that--until just a few years ago--Windows notifications were either nonexistent or (when Windows 8 rolled around) effectively unusable. Fortunately, Windows 10 solved this problem with the Action Center. Let’s go over what the Action Center can do.
You should be well on your way to getting your new computer. We’ve gone over the processor, the memory, the storage, and the display, and should be confident about what you are looking for. For our final part of our computer buying guide, we are going to focus on topics that are important to mention, but maybe didn’t seem to fit in other parts of our guide.
After you’ve got the machine’s core specifications worked out, you then have to turn your attention to your displays. In part four, we take a look at how you are going to broadcast the information from the computer, what you should know about modern displays, and what considerations you need to take.
Most modern gadgets have several different options for storage space, including both internal and external storage. However, the amount of space you’ll need on any given device will depend on various factors. It’s critical that you take these factors into account when purchasing or building a new desktop or laptop.
The second part of our desktop buying guide will focus on RAM, or random-access memory. Many users might not understand the importance of this, or they might have the impression that memory is the same thing as the amount of data your computer stores, which is certainly not true. The truth is that understanding RAM will have a major impact on the way you purchase devices. We’ll help you determine the best options for your device.